📆 On Feb 4th, 2020, Chrome will require third-party cookies to have the SameSite=None and Secure flags. Other browsers (Firefox, Edge) have indicated that they will implement similar changed in the future.
🍪 The Didomi CMP uses 2 cookies to store the user consent status (didomi_token and euconsent).
📰 If you are not sharing consent across domains, the Didomi CMP uses first-party cookies and the new Chrome requirements do not impact you and you have nothing to do.
📰 If you are sharing consent across domains , the Didomi CMP uses third-party cookies and the new Chrome requirements might impact you. Read on to know more about the impact and test that your websites will continue working as expected.
TL;DR: You must ensure that all your visitors are browsing your website with HTTPS enabled. It that is not possible, we recommend disabling consent sharing across domains on websites that are not fully HTTPS.
Impact
When sharing consent across domains, you choose a domain to act as your cookies storage. For instance, privacy.website.com. Domains that are sharing consent (www.website.com and www.other-website.com, for instance), will read and write user consent status through cookies stored on the privacy.website.com domain. Those are considered third-party cookies.
Currently, the cookies written on privacy.website.com by the Didomi CMP do not include the Same Site or Secure flags. After Feb 4th, those cookies would not be accepted by Chrome and the user consent status would be stored locally. While this would effectively disable sharing user consent across websites, user consent would still be collected and stored by domain as the Didomi CMP automatically falls back to storing local consent when it is unable to use third-party cookies for storing consent.
On Jan 28th, 2020, Didomi will release an update to its Web CMP that sets the SameSite=None and Secure flags when writing cookies used for sharing consent across domains. This will comply with Chrome's new requirements and allow consent to be shared across domains correctly.
The main impact is the Secure flag. When set, browsers require the website to be accessed via HTTPS for the cookie to be accepted. As a result: if your visitors navigate your website outside a HTTPS context, consent sharing across domains will not be possible anymore. You must ensure that all your visitors are browsing your website with HTTPS enabled. It that is not possible, we recommend disabling consent sharing across domains on websites that are not fully HTTPS.
It is not possible for the Didomi CMP to not set the Secure flag when setting SameSite=None as that is a requirement of the Chrome specification.
Testing
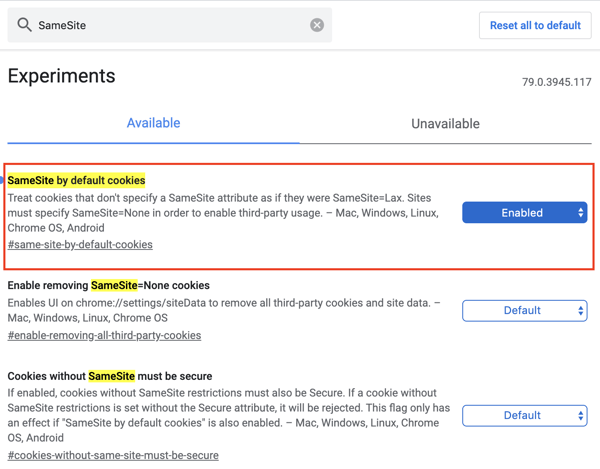
You can test how Chrome behaves with the new SameSite=None requirement by navigating to chrome://flags/#same-site-by-default-cookies in your Chrome browser and enabling the "SameSite by default cookies" experiment:
Before Jan 28th, 2020, third-party cookies should not be created and consent should not be shared across domain when that flag is enabled.
After Jan 28th, 2020 and the Didomi CMP update, third-party cookies will be created as usual and consent will be correctly shared across domains.
Resources
You can learn more about the new Chrome behavior and the SameSite flag on the following websites:
- SameSite cookie recipes (from the Google Chrome team)
- Cookies default to SameSite=Lax