Understand Single Sign-On
What is Single sign-On ?
👉 Single sign-On or SSO is the opportunity for your users to login at once and seamlessly to multiple applications.
Benefits of SSO:
- Eliminating password fatigue and weakness: Instead of using the same weak password in several applications, the user can build and memorize one strong password. And thanks to SSO, the user can seamlessly login to several apps.
- Optimizing user management: One single place (identity provider) where all the user’s accesses to client apps are managed.
SSO is known through two different protocols: SAML and OAuth2 (Social login).
SAML
👉 SAML (Security Assertion Markup Language) is an open standard for exchanging authentication and authorization data between parties. SAML is extensively used by enterprises and governments for sharing identity data in a highly-secured manner.
The data is transferred in XML structure, through HTTP or SOAP mechanisms.
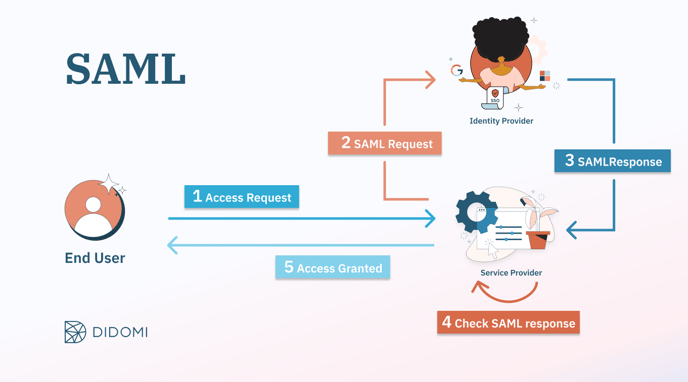
How does SAML work?
The service provider and the identity provider build a trusted relationship, where the user identity is transferred using signed SAML messages instead of passwords.
Social Login
👉 Social login is also a solution for the single sign-on. It consists of reusing the existing login info from a social network like Google, Microsoft, etc. The end user can simply sign in into his social network account without the need to go through the creation flow. Which makes the registration and login easier.
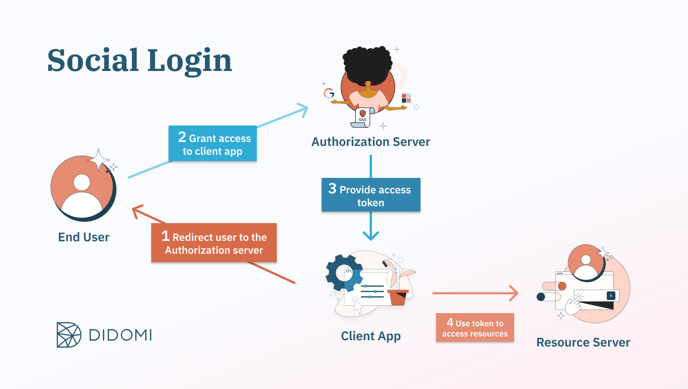
How does Social login work?
Social login is mainly based on OAuth2 protocol.
The authorization server provides the client app with an access token on a specific list of resources. The client app will then use this token to access the authorized resources.
What are the differences between SAML and Social Login?
| Topic | SAML | Social Login |
| Use case | Used for authentication in workspace: system administrators can enforce and control authentication means of their users (e.g. MFA). | Used by individual users to login with their social network account. |
| Security |
Based on signed SAML messages: more secured than the social login. SAML responses are digitally signed. They detect data manipulation in transit and can be encrypted if transport encryption (HTTPS) is insufficient. |
Based on HTTP/HTTPS redirects only. |
| Purpose | SAML is a matter of both authentication and authorization: Verifies user's identity and permissions in order to grant or deny the access to given application. | Social login is a matter of authorization: Controls authorization to a protected resource such as an application or a set of files |